
Rendered Insecure | Proceedings of the 2018 ACM SIGSAC Conference on Computer and Communications Security
![PDF] Stealing Webpages Rendered on Your Browser by Exploiting GPU Vulnerabilities | Semantic Scholar PDF] Stealing Webpages Rendered on Your Browser by Exploiting GPU Vulnerabilities | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/e10443721436b1702c8436a1e3a0bed0cc4892b9/12-Figure13-1.png)
PDF] Stealing Webpages Rendered on Your Browser by Exploiting GPU Vulnerabilities | Semantic Scholar
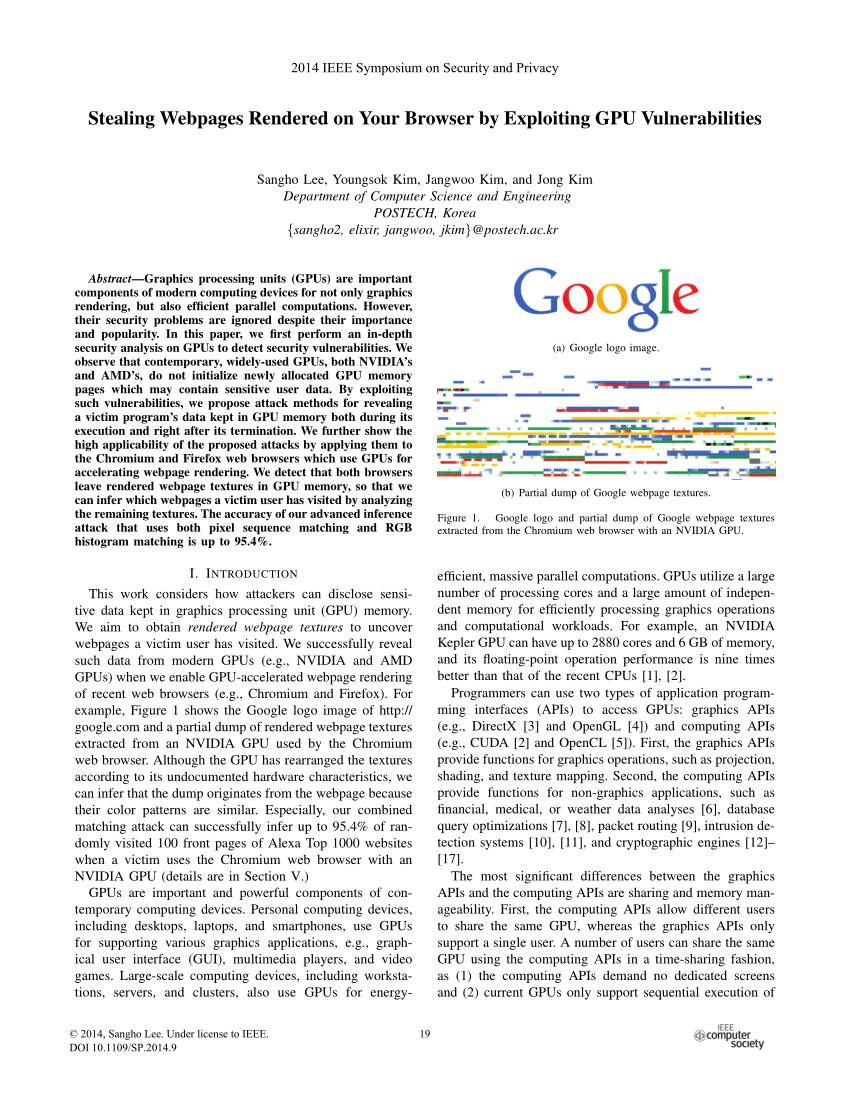
![PDF] Stealing Webpages Rendered on Your Browser by Exploiting GPU Vulnerabilities | Semantic Scholar PDF] Stealing Webpages Rendered on Your Browser by Exploiting GPU Vulnerabilities | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/e10443721436b1702c8436a1e3a0bed0cc4892b9/1-Figure1-1.png)
PDF] Stealing Webpages Rendered on Your Browser by Exploiting GPU Vulnerabilities | Semantic Scholar
![PDF] Stealing Webpages Rendered on Your Browser by Exploiting GPU Vulnerabilities | Semantic Scholar PDF] Stealing Webpages Rendered on Your Browser by Exploiting GPU Vulnerabilities | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/e10443721436b1702c8436a1e3a0bed0cc4892b9/10-Figure10-1.png)
PDF] Stealing Webpages Rendered on Your Browser by Exploiting GPU Vulnerabilities | Semantic Scholar
![PDF] Stealing Webpages Rendered on Your Browser by Exploiting GPU Vulnerabilities | Semantic Scholar PDF] Stealing Webpages Rendered on Your Browser by Exploiting GPU Vulnerabilities | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/e10443721436b1702c8436a1e3a0bed0cc4892b9/10-Figure9-1.png)
PDF] Stealing Webpages Rendered on Your Browser by Exploiting GPU Vulnerabilities | Semantic Scholar
![PDF] Eavesdropping user credentials via GPU side channels on smartphones by Boyuan Yang, Ruirong Chen, Kai Huang, Jun Yang, Wei Gao · 10.1145/3503222.3507757 · OA.mg PDF] Eavesdropping user credentials via GPU side channels on smartphones by Boyuan Yang, Ruirong Chen, Kai Huang, Jun Yang, Wei Gao · 10.1145/3503222.3507757 · OA.mg](https://og.oa.mg/Eavesdropping%20user%20credentials%20via%20GPU%20side%20channels%20on%20smartphones.png?author=%20Boyuan%20Yang,%20Ruirong%20Chen,%20Kai%20Huang,%20Jun%20Yang,%20Wei%20Gao)








![Stealing Webpages Rendered on Your Browser by Exploiting GPU Vulnerabilities [PDF] : r/netsec Stealing Webpages Rendered on Your Browser by Exploiting GPU Vulnerabilities [PDF] : r/netsec](https://preview.redd.it/s6p1so5yck961.png?auto=webp&s=4bfa289078b2a8ac4f95fa4e62d33a151345bd27)
